Pardoning the Samourai Developers Would Restore Legal Clarity and Protect Non-Custodial Code
Bitcoin Magazine
Pardoning the Samourai Developers Would Restore Legal Clarity and Protect Non-Custodial Code
The Samourai Wallet matter raises a fundamental question about how the United States treats non-custodial software and the developers who create it. Keonne Rodriguez and William Lonergan Hill did not operate a financial service or handle customer assets. They wrote and maintained software that allowed users to construct collaborative Bitcoin transactions in a privacy-preserving way. Throughout the tool’s entire lifecycle, users controlled their own keys, initiated their own transactions, and never relied on Samourai or its developers to transmit or safeguard value. The distinction between a custodial service and a non-custodial tool is not a technicality; it is the core boundary that the Bank Secrecy Act, FinCEN guidance, and decades of regulatory practice use to distinguish software authors from regulated financial intermediaries.
This point was reinforced by FinCEN itself. In an internal analysis, the agency concluded that Samourai’s architecture did not constitute money transmission because no third party took possession or control of user funds. That conclusion was never disclosed to the defense while the prosecution advanced a theory that required the opposite: that building software which users employ for privacy is functionally equivalent to operating a financial institution. When that analysis finally surfaced, it confirmed what has long been understood across the industry and within the regulatory community—that non-custodial tools fall outside the BSA’s money-transmitter framework because there is no transfer of value by a third party. The case ultimately treated the developers as if they were responsible for the independent actions of users, even though they had no role in executing, intermediating, or approving any transaction. Some individuals did misuse the tool, as happens with any privacy or security technology, but the law has never equated misuse with liability for the creators. We do not treat the authors of encryption libraries, VPN protocols, or email clients as participants in unlawful activity simply because bad actors rely on those tools. Collapsing the distinction between developing a tool and operating a service would introduce an untenable level of risk for anyone building privacy-enhancing or security-critical software.
There is also an important speech component. Courts have consistently recognized that code is expressive, and publishing open-source software is an act of communication. When publication is treated as evidence of “operation,” the legal boundary between authorship and conduct becomes blurred in a way that threatens a wide range of legitimate technologies. Any precedent suggesting that developers are responsible for unforeseeable downstream use would have immediate consequences for cryptography, cybersecurity research, and open-source work more broadly.
Rodriguez and Hill ultimately accepted plea agreements in the face of substantial sentencing exposure, even though government records undermined the central regulatory theory of the case. Their convictions now rest on a framework that is at odds with established guidance and with the direction in which federal policy has since moved. A pardon would bring the legal outcome back into alignment with the underlying facts: this was software development, not money transmission, and the individuals involved should not bear criminal liability for writing code that users executed independently.
This case has already had a measurable chilling effect on developers working on privacy and security tools in the United States. Leaving the convictions in place would discourage responsible innovation and push critical work to jurisdictions that do not share our commitment to open research and transparent development. A pardon would correct a clear misapplication of federal law, protect the integrity of long-standing distinctions in financial regulation, and reaffirm that publishing non-custodial software is not—and should not become—a criminal act.
Disclaimer – This is a guest contribution by Zack Shapiro, originally published by the Bitcoin Policy Institute (BPI). The views and opinions expressed are solely those of the author and do not necessarily reflect the views of BTC Inc or Bitcoin Magazine.
This post Pardoning the Samourai Developers Would Restore Legal Clarity and Protect Non-Custodial Code first appeared on Bitcoin Magazine and is written by Zack Shapiro.
You May Also Like
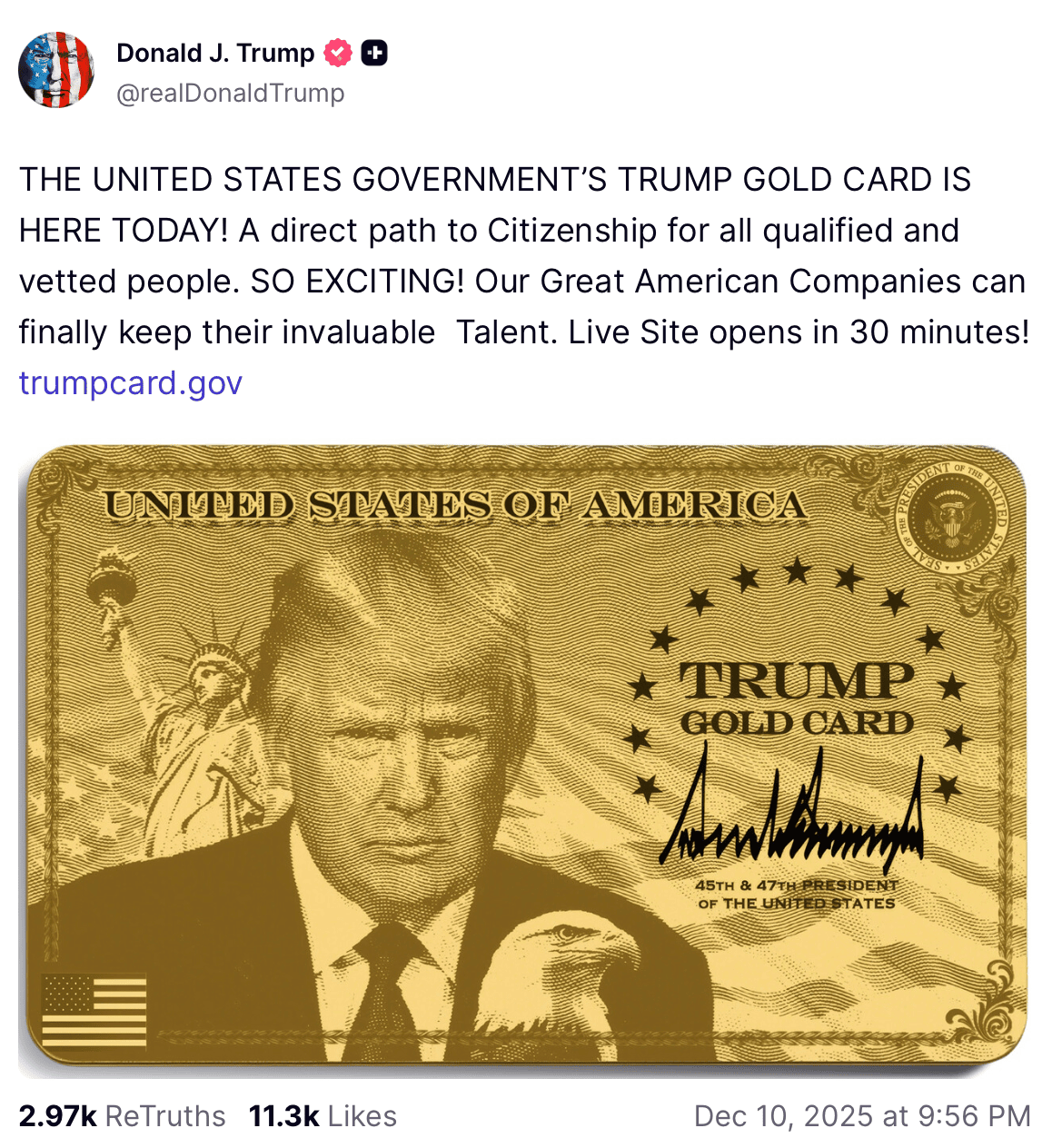
Trump Announced the Launch of the Trump Gold Card

Vitalik Buterin Suggests Ethereum Security Intact Amid Recent Glitch
